Your Keys, Your Control. Hardware-Secured
The Chia Signer app transforms your smartphone into a dedicated security module. Using the Secure Enclave on iOS and Strongbox or the Trusted Execution Environment (TEE) on Android, Chia Signer ensures your spend keys are generated, stored, and protected by hardware-isolated security.
With Chia Signer, your keys never leave your device, and your transactions remain entirely under your control.
Why Use Chia Signer?
Hardware-Rooted Security
Most software vulnerabilities happen at the OS level. Chia Signer mitigates these risks by storing your spend keys in a hardware-isolated environment. Even if your phone’s primary operating system is compromised, your private keys remain inaccessible to external threats.
2-Device Authentication (2DA)
Move beyond simply 2-Factor Authentication. By separating your Chia Cloud Wallet (on your computer or primary phone) from your signing keys (on your dedicated Signer device), you create a physical air-gap for your approvals. To move funds, you must have physical possession of your Signer device.
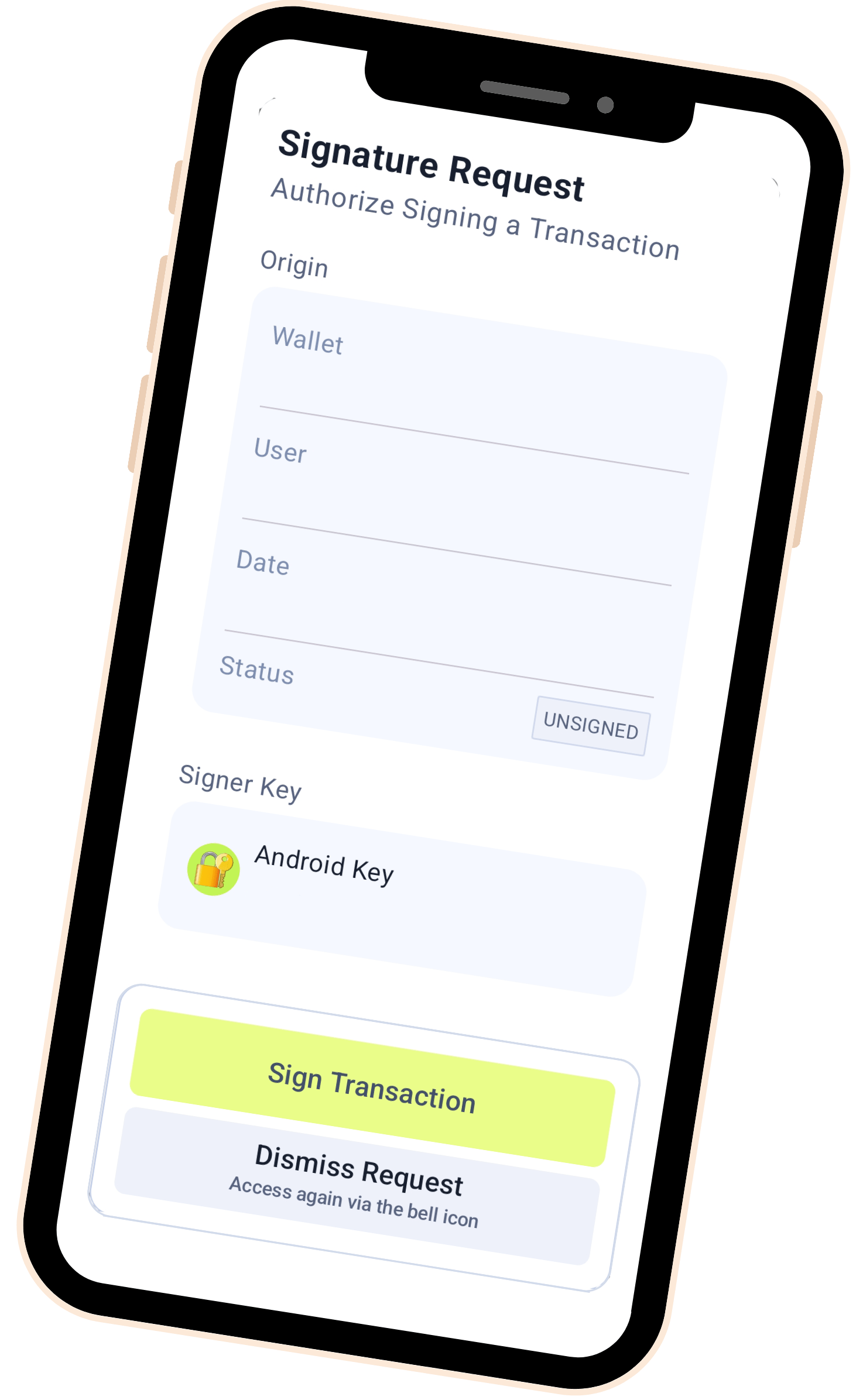
Seamless Transaction Signing
Review and approve transactions with a single tap. Chia Signer uses secure QR code linking and encrypted communication to receive signing requests from your wallet, allowing you to verify transaction details before authorizing them with biometrics (Face ID, Touch ID, or Fingerprint).
Built for the Future of Custody
Whether you are a solo farmer or managing institutional assets, Chia Signer is a core component of the Chia custody ecosystem. It allows for flexible, multi-sig-capable security that scales with your needs.
Looking for more details? Check out our Full Documentation or join the conversation on Discord.